Tackling Leaky Revenues with Smarter Contract Operations

Leaky revenue is essentially money that businesses lose due to various errors like billing...

Catch up on all the latest news, blogs, Ken Adams advice, and more.

Leaky revenue is essentially money that businesses lose due to various errors like billing...

In today's fast-paced business environment, managing contracts efficiently is more critical than...

Contracts are the backbone of business relationships, outlining rights, obligations, and...

Our very own Chief Content Officer and contract expert Ken Adams is back in the news. Last Friday,...

The legal industry is undergoing a transformation, with technology playing an increasingly crucial...
Today someone asked me this in an email message:

Contract Lifecycle Management (CLM) tools are all the rage. Consultants are recommending them....

Kevin Miller, CEO of LegalSifter®️, appears as the featured guest on the Legal Tech StartUp Focus...

Know the essential elements of a contract for it to be legally binding. If one or more of these...

I noted with interest Casey Flaherty's recent post entitled The Limits of Incremental Improvements....
When looking for a solution to expedite their contract review process, particularly one that...
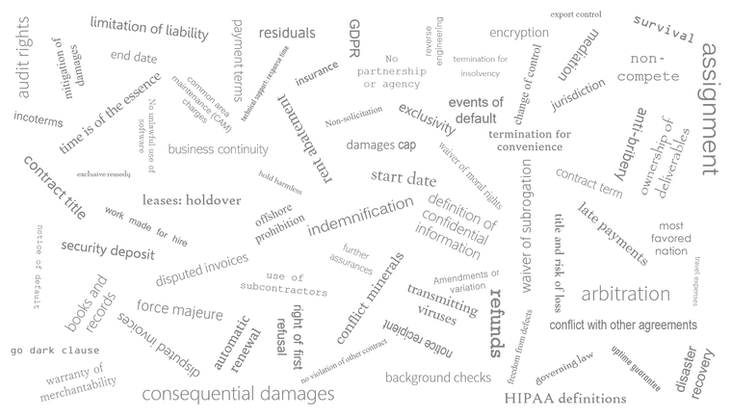
AI contract review allows people to negotiate contracts faster, cheaper, and with better results....
(This piece was first published on the website of LegalSifter partner American Inns of Court.)
